Data Centres as Military Targets: The New INFOWAR
Bottom Line Up Front
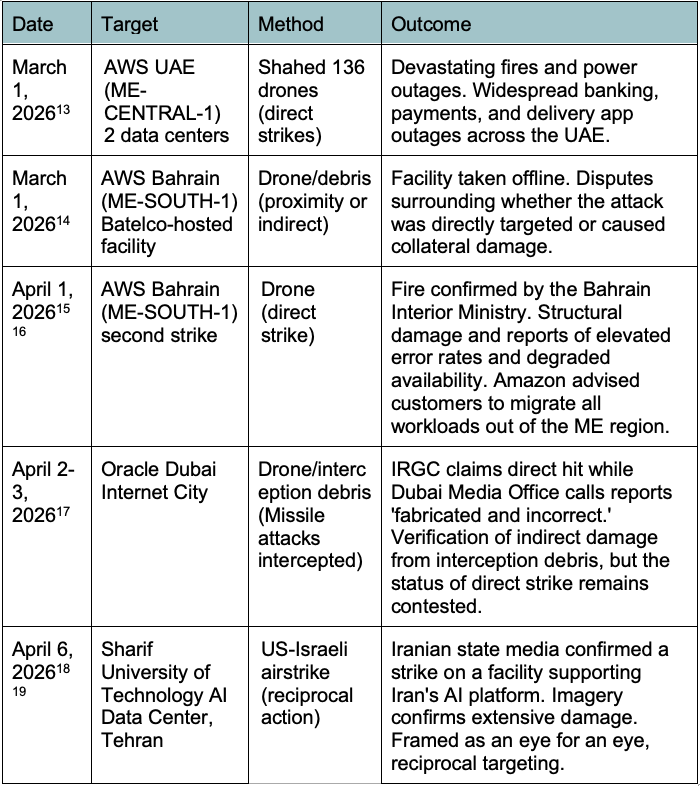
The March 1st Iranian attack against Amazon Web Services data centres in the UAE and Bahrain marked the first time in military history that a state actor has conducted deliberate kinetic strikes against hyperscale commercial cloud infrastructure. This attack was accompanied by a list of 18 additional American technology companies potentially under threat. Targeting has continued, with Amazon and Oracle data centres in Bahrain and Dubai being struck on April 1st-3rd. US and Israeli retaliatory airstrikes on April 6th against the Sharif University of Technology AI Data Centre in Tehran show an eye-for-an-eye approach to infrastructure warfare and elevate the risk of continued aggression in this sector.
The April 7th US-Iran ceasefire has temporarily suspended kinetic attacks, but the threat is far from resolved. The Islamabad peace talks on 11-12 April collapsed without agreement, with Iran stating the US failed to gain its trust and Trump threatening a "full naval blockade." The ceasefire expires on 22 April. Iran has explicitly stated this ceasefire does not end the war, Israeli operations continue across the Lebanon front, and the IRGC's 18-company target list remains published and unretracted. Just four hours before the ceasefire, the IRGC attacked the Jubail petrochemical plant, demonstrating willingness to conduct infrastructure attacks up to the final moment of negotiation. Data centres across the Gulf will return to immediate targeting priority the moment hostilities resume.
Situation Overview
On February 28, 2026, the United States and Israel launched Operation Epic Fury against Iran, a coordinated air campaign targeting Iranian leadership, military installations, missile production facilities, and the remnants of Iran's nuclear programme.
Unlike the June 25th Twelve-Day War, which was limited to nuclear targets, Operation Epic Fury shifted objectives toward the degradation of the Iranian government as a whole. Administrative, military, and dual-use infrastructure became viable targets.
Iran responded with Operation True Promise 4. The IRGC closed the Strait of Hormuz and launched hundreds of drones and ballistic missiles targeted at US bases in Bahrain, Jordan, Kuwait, Qatar, and the UAE.
As the conflict progressed, the targeting parameters of both sides expanded beyond military objectives, growing to include oil and gas infrastructure, civilian infrastructure, critical utilities, and data and cloud storage facilities.
Trump's Escalatory Rhetoric
Throughout the conflict's fifth and sixth weeks, President Trump employed increasingly escalatory rhetoric, reaching a level unprecedented in modern American warfare.
On March 26, Trump set a 10-day deadline for Iran to reopen the Strait of Hormuz, warning of dire consequences. Threats included sending Iran "back to the stone age." By Easter Sunday, April 5th, no major diplomatic breakthrough had been made, and Trump threatened on Truth Social to target and destroy Iranian power plants and bridges if the Strait of Hormuz was not opened.
On April 7th, hours before the ceasefire was announced, Trump posted on Truth Social that "a whole civilization will die tonight" if Iran failed to meet his deadline. Over 100 international law experts signed an open letter warning that attacks on power plants and water infrastructure without distinction between civilian and military targets would constitute war crimes under the Geneva Conventions.
This rhetoric is analytically significant beyond its diplomatic shock value. Trump explicitly threatened energy, water, and bridge infrastructure with the "whole civilization" target, strongly eroding distinctions between military and civilian targets. IRGC statements declare that any destruction of Iranian civilian assets would licence equivalent retaliation against Gulf and US-linked infrastructure. Taken together, these claims establish a framework for the mutual destruction of infrastructure that will directly affect data centres.
Iran's Retaliatory Methodology
The claimed logic behind Iran's escalatory targeting approach has remained fairly consistent throughout the conflict. For every US-Israeli strike on an Iranian economic or strategic asset, a retaliatory strike against a US-linked commercial or industrial target in Gulf partner states would be executed. One example is the IRGC attack on Jubail Industrial City, Saudi Arabia, which was framed as retaliation against an Israel/US strike on Asaluyeh petrochemical plants. When the US-Israeli struck Bank Sepah data centre in Tehran, the IRGC declared that all US and Israeli economic centres and banks across the region are now legitimate targets. Once a targeting threshold is crossed, subsequent strikes against the same category of infrastructure become progressively normalised and operationally easier to justify.
Jubail Industrial City Attack
An April 7th attack reinforces just how real Iranian infrastructure threats are. Approximately four hours before the ceasefire came into effect, the IRGC executed a ballistic missile and suicide drone attack on Jubail Industrial City, Saudi Arabia's largest downstream petrochemical complex.
The Sadra Complex was targeted, a $20 billion joint venture between Saudi Aramco and Dow Chemical. Air defence systems shot down seven ballistic missiles, but direct hits and debris from interceptions caused fires at the plants. Additional facilities in Jubail linked to ExxonMobil, and a petrochemical facility in nearby Juaymah were also struck.
Jubail is a critical node in global energy and manufacturing supply chains, producing steel, gasoline, petrochemicals, lubricating oil, and chemical fertilisers. The proximity of this attack to the ceasefire implementation was a bargaining gesture and demonstration of the IRGC's willingness to strike infrastructure targets. Data centres fall within this same doctrine and targeting logic.
Data Centres
Commercial data centres enable most of the technology that runs the modern world: financial transactions, communications, logistics platforms, government services, military command-and-control, and AI systems for targeting and intelligence. They are valuable, concentrated physical infrastructure whose failure produces immediate cascading economic and military effects. Disruption can pose a threat with similarly devastating effects as the shutdown of traditional high-value targets like ports, rail hubs, power plants, and oil refineries.
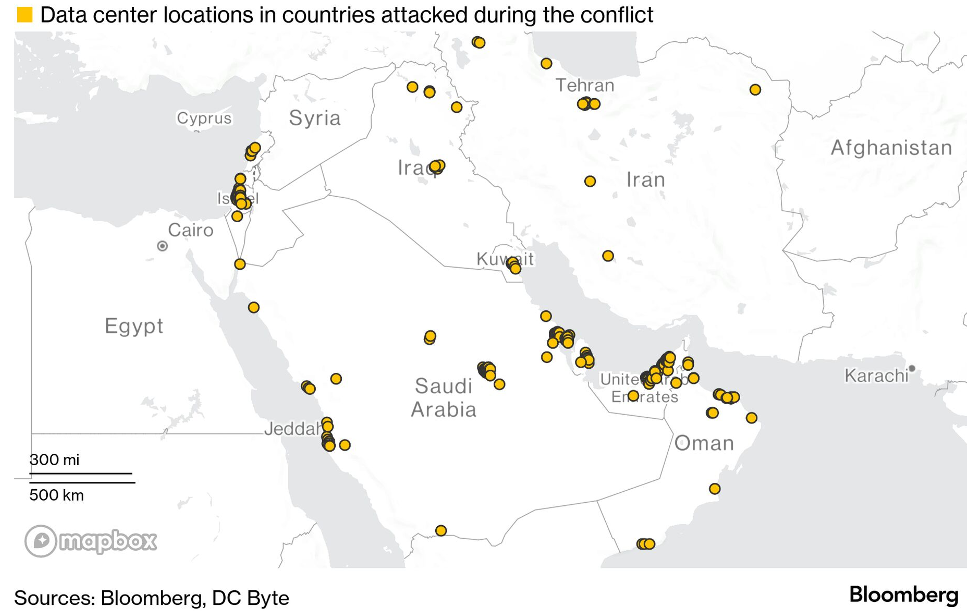
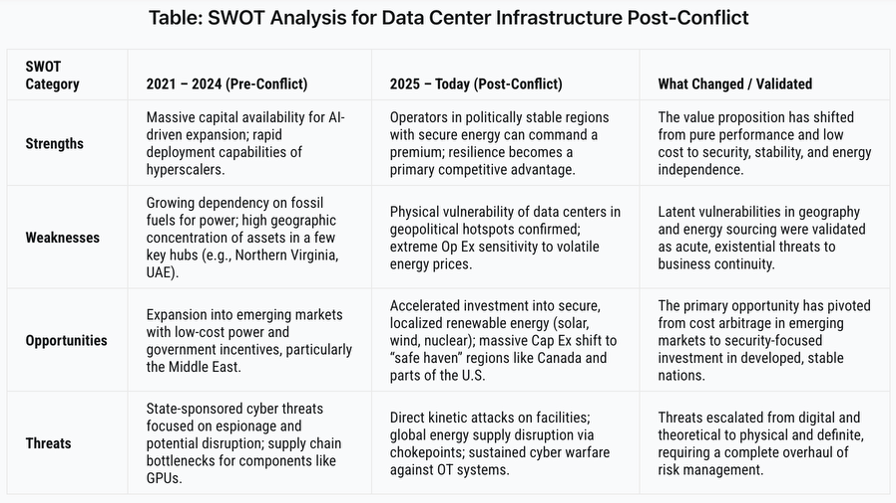
Rising AI-driven compute demand, which is projected to grow 16 percent annually through 2028 and drive up to 180 percent capacity expansion by 2030, has pushed hyperscalers to seek new regions capable of rapid, scalable deployment. The Gulf is emerging as a primary destination, with data centre capacity projected to triple by 2030. The region's abundant capital, state-backed investment, streamlined regulation, and a strategic position linking Europe, Asia, and Africa with strong low-latency connectivity make it the ideal location to meet rapidly growing demand.
Chronology and Overview of Attacks
Data centres have previously been targeted by cyberattacks and espionage efforts, such as the 2024 destruction of data by Ukrainian hackers in a Russian military-affiliated data centre. However, drone and missile attacks on the physical infrastructure of these centres are a development new to Operation Epic Fury.
Significance
In our current day and age, the boundary between commercial cloud computing and military operations has largely vanished. The Pentagon's Joint Warfighting Cloud Capability (JWCC) and Joint All-Domain Command and Control (JADC2) networks run on the same commercial infrastructure that serves banks, ride-share applications, and consumer services. It has been reported that the US used AWS servers to run workloads during the Iran strikes, including target identification, AI-powered intelligence assessments, and battle simulations.
Iranian state television declared the purpose of these attacks was to "identify the role of these centers in supporting the enemy's military and intelligence activities." The United States requires contracted cloud-computing service providers to store data within the United States. Exceptions are only made for sites physically located on Department of Defence premises or authorised by the appropriate official. Whether the AWS facilities actually hosted US military workloads is not publicly confirmed; however, their potential to do so crosses the strategic threshold for plausible justification of strikes.
Legal Framework of Targeting
Under Article 52(2) of Additional Protocol I to the Geneva Conventions, an object is a legitimate military target when it makes an effective contribution to military action, and its neutralisation offers a definite military advantage. The broad scope of this definition means a single significant military function on shared infrastructure can render the entire facility a lawful military objective.
Legal analysis of the March and April 2026 strikes establishes physical co-location as the determining factor. If the military workload provides the legal justification for targeting, the entire building can be lawfully destroyed under LOAC, regardless of how much of its workload is civilian.
This poses a serious challenge to every US tech company operating in the Gulf. Israel's Project Nimbus (a $1.2 billion cloud contract awarded to Google and AWS) explicitly forbids providers from suspending services for political reasons. Actors are contractually required to support state military operations regardless of conflict environment, which may provide legal justification for targeting those facilities under LOAC.
The Cuba Submarine precedent (1898) establishes that during armed conflicts, state actions taken as legitimate acts of war override private property rights without an obligation to compensate affected entities because the private companies' contractual obligations required them to serve official government interests. Under this precedent, any private sector claims against state belligerents for damages from the 2026 strikes face extremely difficult legal standing.
Data centres have become operationally relevant infrastructure in modern conflict. As militaries continue to increasingly rely on cloud computing and AI-enabled systems, the intersection of civilian digital infrastructure and military operations will continue to pose complex legal challenges. Both policymakers and the private sector should prepare for a future where commercial infrastructure is a permanent fixture on the battlefield.
The List
On April 1, 2026, the IRGC published its most explicit and time-bound threat to date via Sepah News and an IRGC-linked Telegram channel. The list named 18 companies as legitimate military targets, framing the action as retaliation for US and Israeli assassination operations against Iranian leadership. Language was clear: "From now on, for every assassination, an American company will be destroyed." Notably, this list excludes Amazon, which has been the primary subject of Iranian attacks. Strikes were announced to begin at 8 PM Tehran time on April 1st. This was not an empty threat, as seen through the attacks on AWS and Oracle servers April 1-3.
The stated justification for these threats was that "American ICT and AI companies are the main element in designing and tracking terror targets." The list includes: Cisco, HP, Intel, Oracle, Microsoft, Apple, Google, Meta, IBM, Dell, Palantir, Nvidia, JPMorgan Chase, Tesla, GE, Spire Solutions, Boeing, and UAE-based G42. The IRGC urged employees to leave their workplaces "immediately to save their lives."
Weeks prior, on March 11th, the IRGC-affiliated Tasnim News Agency published a list of thirty specific facility locations across the Middle East. Targets, identified as "enemy technology infrastructure," included data centres, research offices, cloud regions, and defence-linked operations. Several locations in Tel Aviv, Dubai, Abu Dhabi, Doha, and Jerusalem were named.
The 18-company target list remains published and unretracted as of 13 April. The ceasefire has suspended but not removed the operational framework behind it.
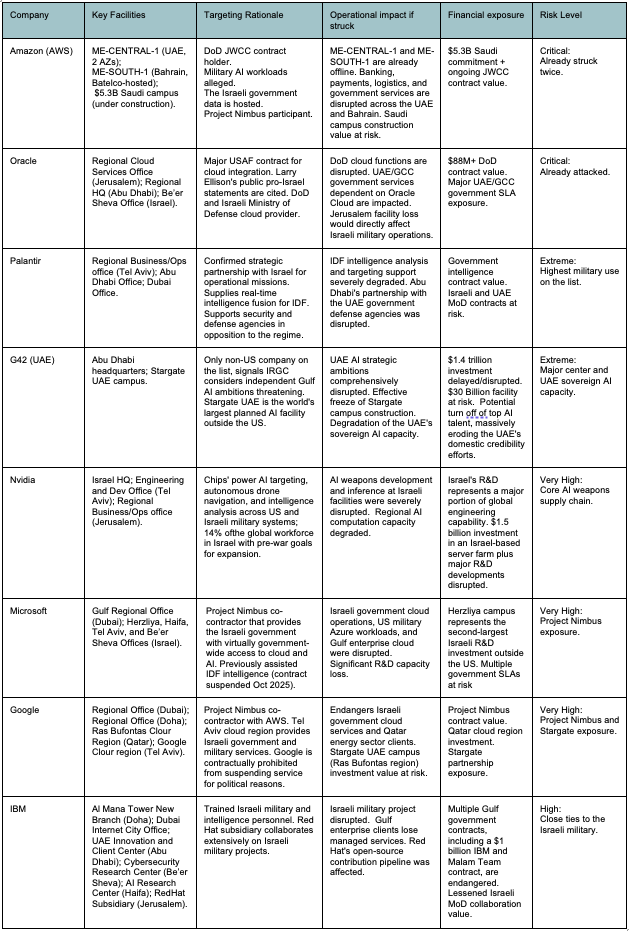
AI Investment in the Gulf
The companies on the IRGC list represent the collective core of a multi-trillion-dollar US-Gulf AI infrastructure project. U.S. President Donald Trump's 2025 tour of the region generated more than $2 trillion in investment pledges, including the planned Stargate UAE campus in Abu Dhabi, which would be the largest AI facility outside the United States. According to analysts at TD Cowen, in 2026, hyperscaler capital expenditure is forecast to exceed $600 billion, with roughly 75 per cent tied to AI infrastructure.
The crown jewel of this investment, the Stargate UAE campus in Abu Dhabi, includes participation from G42, OpenAI, Oracle, NVIDIA, and Cisco. A successful strike on even one of these partners' regional facilities would effectively freeze or terminate the project. The Stargate site itself has also been labelled a target, with Iran's Khatam al-Anbiya Headquarters posting a video on X on April 3rd claiming, "Nothing is hidden from our sight. All ICT companies in the region will be considered legitimate targets for us." The video then zoomed into the Abu Dhabi Stargate site. IDC's March 2026 revised forecast cut global IT spending growth from a pre-conflict estimate of 6.8% to 4.5%, reflecting widespread postponement of technology investments across the region.
Data centres require a robust power supply to meet their energy needs, adding another layer of structural vulnerability. A data centre with intact servers but no reliable electricity is a disabled asset. Iran's attacks on Gulf power plants, desalination facilities, and petrochemical infrastructure indirectly target data centres, as these facilities provide the electricity and water required by data centre campuses.
Currently, the structural advantages that drew tech companies to the Gulf (cheap energy, abundant funding, and a strategic location) remain intact. However, continued attacks on data centres pose a serious problem for the viability of AI and data infrastructure in the Gulf.
Role of the Ceasefire
During the two-week ceasefire window, kinetic attacks on data centres are suspended. Financial markets initially reacted with significant relief, with oil futures falling more than 13% to below $92 per barrel within an hour of Trump's announcement. Prices have since climbed back above $100 per barrel as belief in the ceasefire's durability erodes.
The Islamabad talks on 10-12 April were the first structured diplomatic framework capable of producing a durable end to hostilities. VP Vance, Witkoff, and Kushner led the US delegation. Parliament Speaker Ghalibaf, Foreign Minister Araghchi, and SNSC Secretary Ahmadian led the Iranian side. On April 12, Vance departed Pakistan stating no agreement had been reached. Ghalibaf said the US failed to gain Iran's trust. Trump subsequently threatened a "full naval blockade" of Iran. The ceasefire expires on April 22, with no further talks currently scheduled.
While the ceasefire technically holds between the US and Iran, its central condition, the "complete, immediate, and safe opening" of the Strait, has not been met. In the days following the ceasefire announcement, just seven ships passed through the Strait in a 24-hour period compared to around 140 normally, with only one being an oil products tanker. Iran's Ports and Maritime Organisation directed ships to use alternative shipping routes to avoid potential naval mines in the main traffic zone.
Within hours of the ceasefire announcement, there were already a multitude of violations. Israel struck 100 targets in Lebanon, killing at least 254 people. Iran's 10-point plan explicitly includes Lebanon in the ceasefire agreement, prompting the IRGC to briefly re-close the Strait of Hormuz. The first days of the ceasefire were the deadliest seen in Lebanon since September 2024, with at least 357 dead and 1,223 injured in Israeli strikes according to Lebanon's Ministry of Health.
Several Gulf states were also attacked following the ceasefire implementation, with Saudi Arabia, Bahrain, Kuwait, Qatar, and the UAE all reporting attempted strikes. Due to the decentralised nature of the IRGC command structure, it is plausible these attacks were carried out before cessation orders were received.
The two sides' foundational proposals remain structurally incompatible.
Iran's 10-point plan demands:
- Iranian dominance and oversight of the Strait of Hormuz
- Full withdrawal of US combat forces from all regional bases
- Lifting of all primary and secondary sanctions and UN resolutions
- Compensation in the form of reparations
- The right to nuclear enrichment
The US 15-point plan demands were never made public but are reported to include:
- Full nuclear facility dismantlement
- Limits on Iranian defence capabilities
- An end to all proxy networks
- The unconditional reopening of the Strait
There are major points of contention between these proposals with little room for compromise. Both states have framed enrichment as a non-negotiable red line, with compromise by either side domestically unpalatable. The Islamabad talks confirmed this impasse. The divergence between the two frameworks, combined with early violations and unresolved trigger points, results in a framework that may reduce immediate escalation but is unlikely to endure beyond the near term.
Without a lasting ceasefire, danger to data centres and cloud storage facilities remains. The conditions that made data centres targets have not changed. Commercial cloud infrastructure is still deeply entangled with military operations and physical segregation of military and civilian workloads has not (and could not have) been implemented. The IRGC target 18-company list remains published and unretracted, with no signs showing the document as anything other than operational.
Cyber Threat Escalation During Ceasefire
Cybersecurity experts have warned that the ceasefire is likely to increase rather than decrease threats to US tech companies. IRGC-linked hacking group Handala stated it would temporarily postpone attacks on the US but would continue targeting Israel and would revive efforts against America "when the time was right." The group explicitly stated: "The cyber war did not begin with the military conflict, and it will not end with any military ceasefire."
On April 8, US authorities issued a joint FBI/NSA/CISA advisory warning that Iranian hackers have infiltrated programmable logic controllers and SCADA systems across US critical infrastructure sectors including ports, power plants, and water facilities. Cybersecurity analysts assess that the ceasefire lull may allow Iranian cyber operators to shift from regional targets to deeper infiltration of US organisations that participated in the war effort, including data centres, tech companies, and defence contractors. This cyber dimension means the threat to data centre operations persists even while kinetic attacks are paused.


Responses